Gain complete visibility into employee activity across devices and applications
Email and chat communications
Web browsing and application usage
File transfers and downloads
Screenshots of user actions

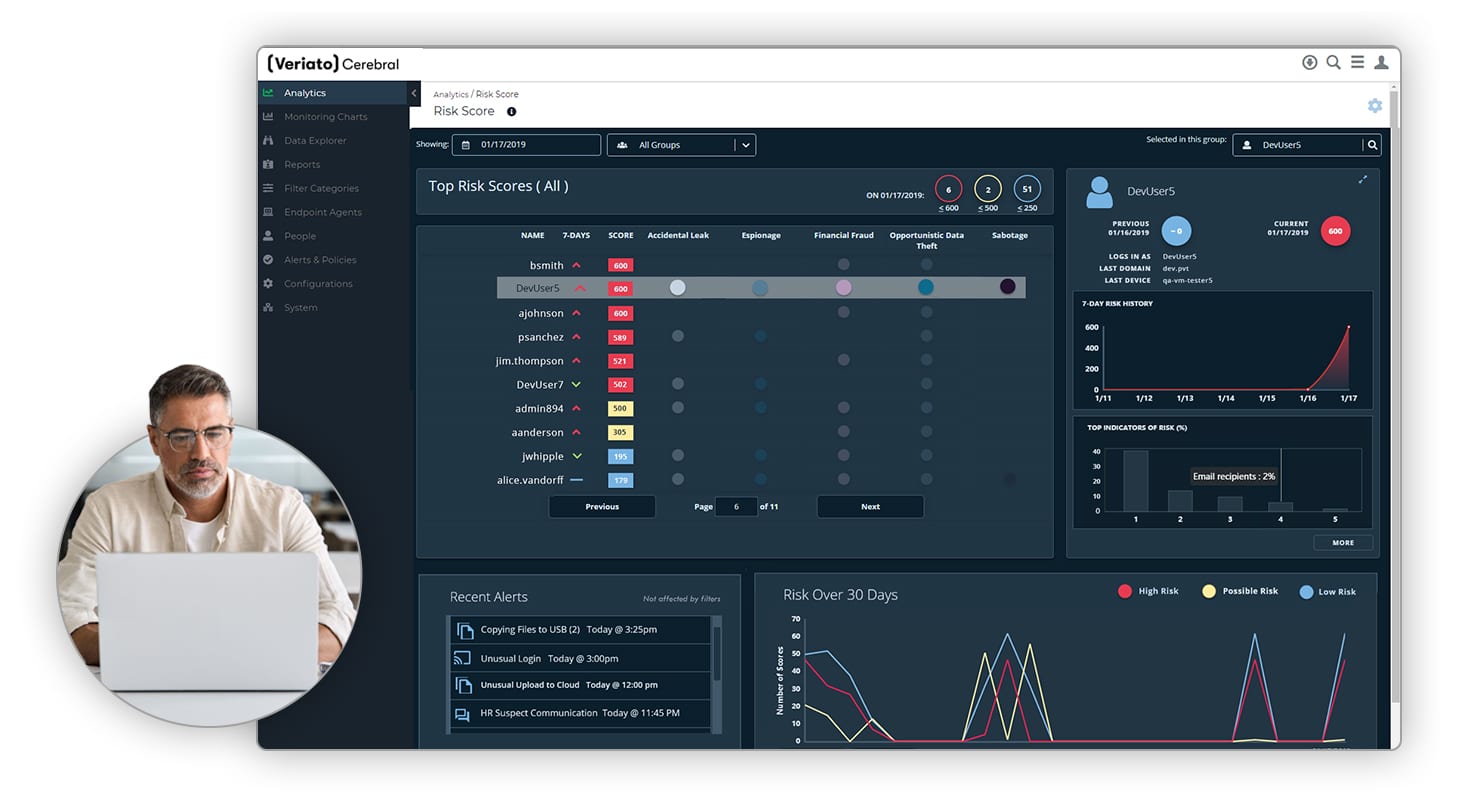
Risk Scoring and Alerts
Utilize AI-driven user and entity behavior analytics (UEBA) to:
- Assign risk scores to employees based on behavioral patterns
- Detect anomalies that signal potential threats
- Generate real-time alerts to address risks proactively

Sentiment Analysis
Identify and categorize opinions expressed in email text using computational linguistic analysis.
- Detect signs of dissatisfaction or burnout
- Understand changes in sentiment over time
- Pinpoint disgruntled workers and possible security risks
Detailed Reporting and Investigation Tools
Simplify compliance audits and workplace investigations with:
- Comprehensive data logs
- Visual evidence through screenshots
- Customizable reports for quick and easy analysis
Insider Threats Continue to Grow
82%
Of data breaches are caused by unsecure behavior by employees, according to Gartner.
$4.45M
The average cost of a data breach in 2023, an increase of 15% in 3 years, according to IBM.
85 Days
The average time to contain an insider incident, per recent report by the Poneman Institute.
How It Works
Implementing Veriato Cerebral is simple and straightforward:
1. Data Collection
Deploy the Cerebral agent to user devices to capture real-time activity data across more than 60 activity types.
2. Behavior Analysis
Use AI-powered analytics to detect patterns, anomalies, and potential risks.
3. Alert Generation
Receive customizable, real-time alerts for suspicious or risky activities.
4. Reporting & Insights
Generate detailed reports and visual evidence for audits, investigations, or compliance reviews.
Benefits of Veriato Cerebral
Proactively detect and mitigate insider threats before they escalate.

Enhanced Security
Proactively detect and mitigate insider threats before they escalate.

Improved Productivity
Identify unproductive behaviors and ensure employees stay focused.

Simplified Compliance
Maintain a transparent and fair workplace while meeting regulatory requirements.
Let’s Get Started
What Clients Have to Say
Why Choose On-Premises Deployment?
Veriato Cerebral is exclusively available as an on-premises solution, providing:
Full control over your data
Enhanced privacy and security
Compliance with strict regulatory standards
Take Control of Insider Risk Today
Veriato Cerebral is your trusted solution for insider risk management. Schedule a demo or contact our team to learn how we can help protect your business.
Common Insider Risk Management Questions
What Are The Signs Of Insider Threat?
There are several activities that could indicate someone is an insider threat. You may have an insider threat if an employee:
- Grants themselves access to more privileged information.
- Begins to access privileged information more often.
- Accesses privileged information that they should not need to access to perform their job duties.
- Prints a lot of documents or begins downloading data onto a personal USB.
- Uses a weak password.
- Leaves their computer on without logging off or exiting applications with sensitive information.
These behaviors are red flags that every company should take seriously to prevent a cyberattack.
How Do I Mitigate Insider Threats?
Here are the five steps you should take to reduce the risk of insider attacks within your organization:
- Identify your most valuable assets, so you know what needs to be protected.
- Establish an insider threat program that outlines how you will monitor employees and detect insider threats.
- Begin monitoring employees and analyzing user data to identify suspicious activity.
- Enforce the rules and the consequences for failing to comply with company policy.
- Conduct cybersecurity training with your employees to ensure they know what they can do to prevent an attack and the consequences of maliciously committing an attack.
What Are The Building Blocks Of A Successful Insider Risk Management Program?
Because you never know where an attack will come from, it’s critical that every endpoint is protected from both external and internal attacks. Typically, a robust security strategy incorporates the following capabilities:
- User & Entity Behavior Analytics (UEBA)
- User Activity Monitoring (UAM)
- Data Breach Response (DBR)
- Data Loss Prevention (DLP)
Veriato’s platform incorporates most of these capabilities under one roof, powering everything with proprietary machine learning capabilities.
Why Do I Need An Insider Risk Management And Detection Solution?
An insider threat management solution like Veriato will help you monitor your most sensitive data, track user activity and monitor for potential breaches before they happen. It will also help you ensure regulatory compliance, conduct audits and respond quickly to any data breaches.
Veriato can help you take your insider risk detection a step further and proactively monitor for threats by using machine learning to analyze user behavior, identify risk factors and generate risk scores for each monitored user.
What Is Insider Risk Management?
Insider Risk Management (IRM) is a strategic approach designed to mitigate risks posed by insiders—employees, contractors, or any individuals with access to an organization’s internal resources. It involves identifying, assessing, and managing potential threats that insiders could pose to the confidentiality, integrity, or availability of the organization’s information assets.
What Insider Risk Challenges Are Faced In Business?
Businesses, regardless of size, face significant insider risk challenges:
- Small and Medium-sized Businesses (SMBs) often struggle with limited resources to implement comprehensive IRM strategies, making them vulnerable to threats from negligent or malicious insiders.
- Larger Enterprises deal with the complexity of monitoring a vast number of employees across multiple locations, increasing the difficulty of detecting insider threats amidst the noise of everyday activity.
Both SMBs and larger enterprises must navigate the challenges of balancing security measures with maintaining an open and collaborative work environment.
Why is Insider Risk Management Important?
Insider Risk Management is crucial for safeguarding an organization’s critical assets from the potential threats posed by insiders. It helps in:
- Protecting Sensitive Information: Ensures that confidential data remains secure from unauthorized access or leaks.
- Maintaining Compliance: Assists in adhering to regulatory requirements and avoiding legal penalties.
- Preserving Reputation: Prevents incidents that could damage the organization’s public image and stakeholder trust.
- Enhancing Security Posture: Moves from a reactive to a proactive approach in identifying and mitigating security threats.
What Industries Are Susceptible to Insider Risk Threats?
Insider risks are a critical concern across various sectors, with certain industries being particularly vulnerable due to the nature and sensitivity of the information they handle. Here’s a summary of key sectors at risk:
- Finance Sector: Financial organizations, including banks and investment firms, face insider threats related to embezzlement, fraud, and data breaches, necessitating strong safeguards.
- Healthcare Industry: With strict privacy laws like HIPAA, healthcare providers must protect patient records from unauthorized access or accidental sharing.
- Government Entities: Sensitive PII and PHI data requires stringent clearance and monitoring to prevent data leaks.
- Education Institutions: Strategies to detect and deter breaches are needed in open environments that store student information and intellectual property.
- Technology Companies: The protection of proprietary data, such as source code, is vital to prevent loss to competitors or unauthorized public disclosure.
- Law Firms: Confidential client information must be securely managed to maintain privilege and prevent reputational damage.
- Manufacturing: Trade secrets, especially in defense and high-tech, must be guarded against industrial espionage and internal breaches.
- Retail and E-Commerce: Consumer data integrity and confidentiality must be ensured to protect against internal misuse or tampering.
- Pharmaceutical Companies: Protecting sensitive trial data and research findings is crucial to maintaining competitive advantage and ensuring public safety.
What Are The Key Features of Our Insider Risk Management Solution?
Veriato Insider Risk Management takes user activity monitoring (UAM) to the next level by combining it with AI-powered behavior analytics (UEBA) to help organizations get ahead of insider cyber security risks.
- Power of Generative AI: We use generative AI to interpret advanced behavior signals, like tone, sentiment and use of PII/PHI data. These behavior signals are then combined with activity data to create risk scores for each user. The product learns continuously, improves threat detection and minimizes alert fatigue.
- Easy-to-Use UI: The user interface is simple, intuitive and highly customizable. A non-technical user can navigate it without requiring help from an IT team.
- Minimal Footprint: Collect critical user activity data with minimal footprint and endpoint performance impact.
- Flexible Deployment: Deploy Veriato to fit your needs and regulatory requirements – cloud, on-premise, hybrid. Veriato can monitor a variety of devices, including Windows, Mac and Android.
How Do I Get Started with Veriato?
- Recognize Your Organization’s Needs: Understand the specific insider risk management requirements of your organization.
- Schedule a Demo: Arrange for a demonstration to see how Veriato can assist your organization in staying ahead of potential risks with its AI-driven behavior analysis and comprehensive risk scoring.
- Review Proactive Monitoring Capabilities: Evaluate our proactive monitoring capabilities to ensure they meet your organization’s needs.
- Implement Veriato: Confidently deploy our solutions to manage and mitigate insider threats, safeguarding the safety and integrity of your critical information assets.
Other Frequently Asked Questions
What measures does Veriato take to ensure user privacy while monitoring for insider threats?
Our customers have full control over what data is being collected and how it is stored in order to meet relevant company policy and regulatory requirements. The most effective insider risk management programs combine activity monitoring with transparent communication and employee cybersecurity training.
Can Veriato’s Insider Risk Management Solution be customized for specific industry needs?
Veriato is designed to be highly customizable, allowing it to meet a variety of business requirements. You have full control over what user activity data is being collected and how it is stored. There are hundreds of dashboards and reports to choose from and alert parameters are fully customizable.
How does Veriato help in complying with regulations like HIPAA or GDPR?
We assist organizations in maintaining compliance with regulations such as HIPAA in the healthcare sector and GDPR in the European Union by providing tools for monitoring access to sensitive information, detecting unauthorized data sharing, and generating audit trails. This helps organizations prevent data breaches and ensure that their data handling practices comply with legal requirements.
What role does employee training play in preventing insider threats?
Employee training is crucial in preventing insider threats, as it raises awareness about the importance of data security, familiarizes employees with company policies, and educates them on recognizing and reporting suspicious activities. Regular training sessions can significantly reduce the risk of accidental insider threats.
What is the first step in establishing an effective insider risk management program?
The first step in establishing an effective insider risk management program is conducting a comprehensive risk assessment to identify potential insider threats specific to your organization. This involves mapping out critical assets, understanding which insiders have access to these assets, and determining the potential impact of various threat scenarios.




